-
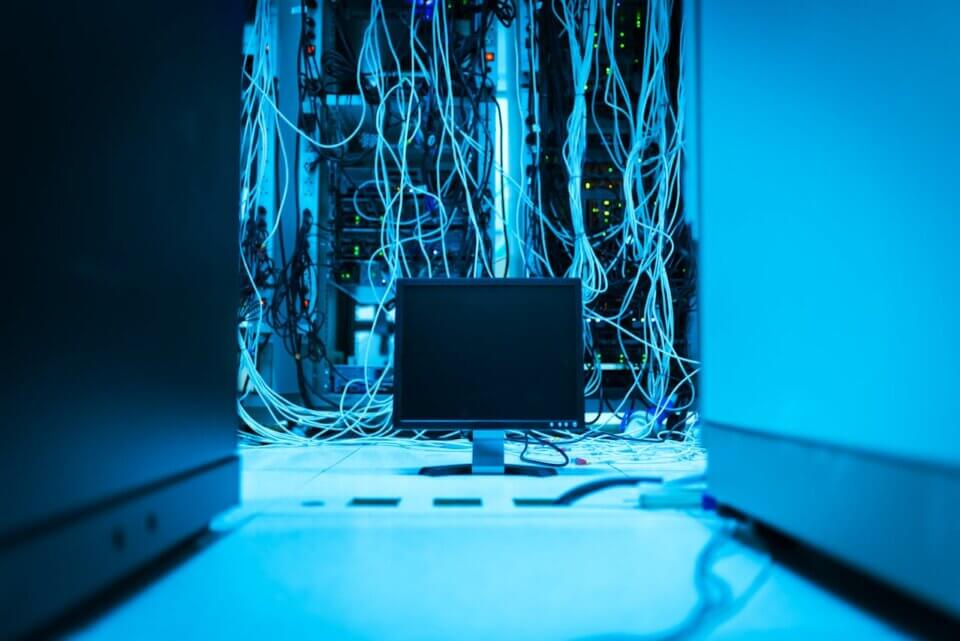
Managed IT Support
View All Managed IT Support
Managed IT Support
Otto IT provides proactive Managed IT Support to keep your business running smoothly with fast, reliable, and tailored tech solutions.
-
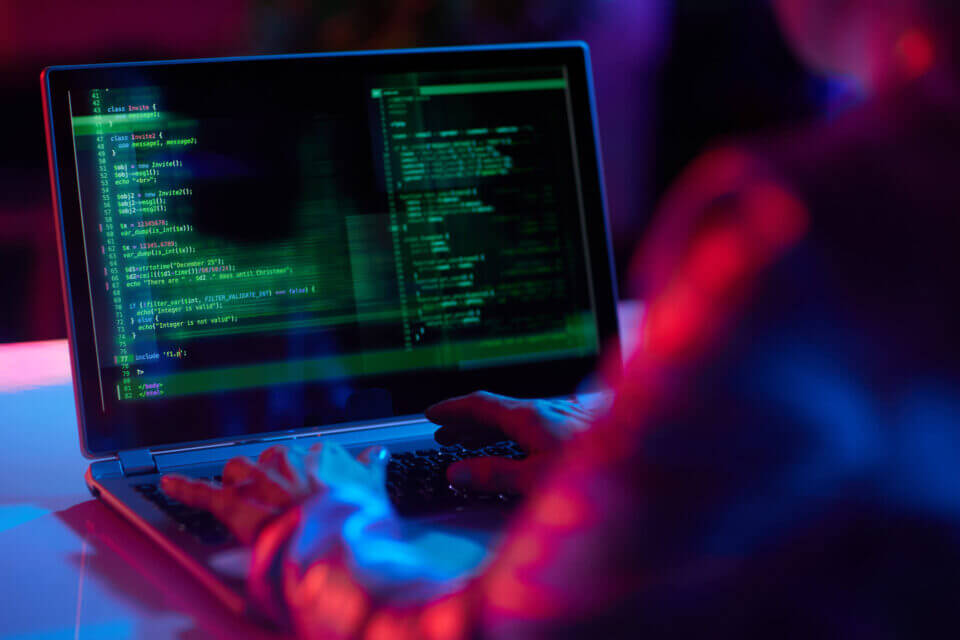
Managed Cybersecurity
View All Managed Cybersecurity
Managed Cybersecurity
Otto IT delivers fully managed, 24/7 cybersecurity through a proactive Security Operations Centre—offering real-time threat detection, rapid incident response, compliance support, and comprehensive endpoint and network protection.
-
Disaster Recovery & Business Continuity
View All Disaster Recovery & Business Continuity
Disaster Recovery & Business Continuity
Otto IT delivers proactive, 24/7 managed cybersecurity via a dedicated Security Operations Centre—offering real-time threat detection, rapid incident response, compliance support, and full endpoint & network protection.
-
Managed Voice & Communications
View All Managed Voice & Communications
Managed Voice & Communications
Otto IT’s UCaaS delivers a cloud-based unified communications platform—integrating VoIP, video, messaging, and collaboration—offering scalable, cost‑efficient, remote-ready connectivity with seamless integrations like Microsoft Teams and CRM systems
-
Managed Cloud Services
View All Managed Cloud Services
Managed Cloud Services
Otto IT’s Managed Cloud Services provide end-to-end cloud infrastructure management—including migration, optimisation, monitoring, backup, and security—ensuring scalable, cost-effective, and high-performance cloud environments.
-
AI, Automation & Strategic Consulting
View All AI, Automation & Strategic Consulting
AI, Automation & Strategic Consulting
Otto IT helps you move beyond traditional transformation by putting AI and intelligent automation at the centre of your strategy. We work with you to uncover opportunities, streamline processes, modernise workflows, and make smarter use of your data, so your teams can move faster, your operations run smoother, and your organisation is set up for what’s next. It’s practical, commercially-minded consulting that turns emerging technology into real business advantage.
- IT Procurement Services
Can’t find what you’re looking for? Call 1300 688 648 for expert IT assistance